Business Email Compromise (BEC) attacks
Business Email Compromise (BEC), formerly known as Man-in-the-Email scams are a blended Spear-phishing attack. BEC attacks follow similar traits to phishing, technical subterfuge with social engineering.
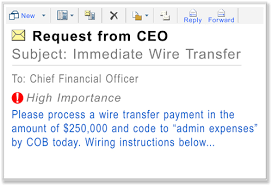
BEC threats actually compromise legitimate business email accounts in order to conduct unauthorised transfer of funds to criminal controlled bank accounts. Essentially the employee of the business is tricked into making a bank transfer, such as paying an attached fake invoice.
BEC scams usually start by compromising an executives email account. The attackers compromise the legitimate email account by using malware such as a key logger or via phishing based methods. Alternatively, the attackers create a domain that’s similar to the company they’re targeting, or use a spoofed email that tricks the target into providing account details. The perpetrators often perform a fair amount of research in order to determine an exploit, such as who initiates money transfers and who requests them, a traveling executive, change in leadership team or similar vulnerability that they can exploit.
The attacker will then submit a bogus invoice or request the victim to make a time critical transfer to a fraudster controlled bank account. Messages can be sent to multiple vendors identified from the employee’s contact list. The business may not become aware of the scheme until their vendors follow up to check for the status of the invoice payment.
The scam mostly banks on social engineering, and typically doesn’t need a sophisticated system penetration. Unlike phishing scams, the emails used in BEC scams are not mass-emailed to avoid being flagged as spam – hence can be problematic to detect and monitor.
The victims are tricked into doing the transfers, via classic social engineering, often stating that the victim should act quickly or in confidence when transferring funds.
The FBI has recently stated that BEC scams have already cost US victims nearly $750 million dollars since 2015 – so yes this is a real threat that we all need to be aware of. Usually these emerging threats will start in one country like the US and then spread to other geographies so let us all watch this space.
In terms of protection the business must – verify any changes in vendor payment locations by using a secondary sign-off by company personnel, educate and train employees and carefully scrutinize all emails.
To start with the business is best placed to protect themselves from malware and spear phishing based attacks.